I went down the pathway of studying for a Master's in Public Policy after 20 years in Technology and Operations for a very real reason: because there aren't enough people who understand how government policies truly impact technology. The problem inherent in this is you have two camps: Policy makers who outsource consulting work to technologists, bridging the gap in commissioned ways that usually reinforce outcomes they're already leaning towards, and technologists who offer often unheeded warnings that end up being cited after the fact, when things go wrong.
As both a technologist and a person of Māori descent, this matters greatly to me, because Māori are in a unique position of vulnerability within New Zealand. The Treaty of Waitangi empowers us to seek redress if we're not treated in an equal fashion to British colonials. But it also creates a position of reliance and dependence, where we look towards government officials to keep the mandates within the Treaty within scope, and appropriately considered.
Bridging the gap is therefore important, especially when it comes down to discussions that involve the way technology will directly affect Māori people.
When Te Mana Raraunga talks about Māori Data Sovereignty, they frame it as inherent Māori rights and interests in how Māori data gets collected, owned, stored, accessed, analyzed, used, reused, and protected. They also separate “sovereignty” from “governance,” (Kukutai & Taylor, 2016; Walter & Suina, 2018) where governance covers the structures, accountability mechanisms, legal tools, and policies that enable Māori control in practice (University of Otago, 2018).
That distinction matters because “sovereignty” language can sound like moral recognition, while “governance” implies infrastructure, staffing, policy, security engineering, vendor management, training, auditing, and dispute resolution. So if the Crown or major institutions say “we respect data sovereignty,” but the implementation pathway assumes iwi and community institutions will carry governance obligations without sustained resourcing, the outcome tends to look like responsibility transfer more than self-determination.
Two related frames help here:
- CARE Principles (Collective benefit, Authority to control, Responsibility, Ethics) push governance toward Indigenous authority and community benefit rather than extractive reuse. They also implicitly require capability because “Authority to control” doesn’t happen through vibes (Carroll, et al., 2020).
- Kukutai’s EMRIP paper makes a blunt point: Indigenous Data Sovereignty becomes real through Indigenous data governance initiatives, and those initiatives can be adopted by the organizations that hold Indigenous data, not just Indigenous peoples themselves. That tends to pull a lot of implementation labor into the “governance” zone (Kukutai, 2024)
Māori researchers working with administrative and linked data in Aotearoa have described how official administrative data has historically served government purposes more than Indigenous agendas, and how participation requires significant technical capability, training, and sustained investment (Theodore et al., 2023). In other words, “use the data” often translates into “fund a skilled team, fund secure environments, fund governance, then negotiate access through state-controlled criteria,” and that’s before a single Māori outcome gets improved (Theodore et al., 2023).
New Zealand’s Current Digital Direction Carries Risk
New Zealand’s digital direction increasingly leans toward digital-first identity and verification, plus deeper use of linked administrative data and automated decision systems, and that combination can create harm when convenience for institutions turns into cost and friction for people. Māori Data Sovereignty and Indigenous Data Sovereignty scholarship frames the core risk as a governance-capability gap: rights and principles only carry weight when communities have real authority, resources, and technical capacity to control collection, linkage, reuse, and downstream decisioning (Kukutai & Taylor, 2016; University of Otago, 2018; Cotter, 2018; Carroll et al., 2020).
In practice, digital exclusion and device dependence can make “optional” digital channels feel mandatory, while Māori entities risk becoming the default support layer for exceptions and failures without matching resourcing, which then feeds the same deficit narratives these sovereignty frameworks were built to prevent (Theodore et al., 2023; Brown et al., 2024).
Digital Identity Regulation (Trust Framework)
NZ now has an opt-in regulatory scheme around digital identity services through the Digital Identity Services Trust Framework Act 2023, which multiple independent analyses describe as setting a “trust framework” for accredited digital identity providers and relying parties (Erdélyi & Erdélyi, 2024; MinterEllisonRuddWatts, 2024)
The DIA discussion paper gives a clean summary of what the framework was designed to do: enable trusted digital identity services, establish a Trust Framework Board and Authority, and include a Māori Advisory Group that advises on tikanga-related matters and engagement with iwi and hapū when needed (Department of Internal Affairs, 2023).
Separately, the Privacy Commissioner’s submission on the Trust Framework Rules stresses that Privacy Act obligations apply across the whole rules structure, and it highlights requirements like revocation requests for credentials. That matters because credential systems inevitably create messy edge cases involving lost devices, coercion, identity disputes, and caregiver control (Privacy Commissioner, 2024). These compound any digital mandates around identification, raising questions about access and accountability that need to be answered before change is introduced.
“Identity Apps” and “Digital Wallets”
Late 2025 reporting framed the launch of the Govt.nz app as an early step toward a government-backed “digital wallet” capable of holding identity credentials, with digital driver licenses repeatedly singled out as a near-term target (1News, 2025; Mathias, 2025c; Radio New Zealand, 2025). That framing matters because adoption pressure rarely waits for the fine print: even when participation stays formally “optional,” vendor and frontline-service expectations can shift toward faster app-based checks, and early coverage already flagged basic device-eligibility friction (for example, users reporting their phones didn’t meet security requirements) that tends to map onto income, age, and care dependence (Mathias, 2025a).
In the broader digital-identity literature, wallet-based identity models routinely change how public and private organizations authenticate people and transact, and those shifts bring governance and exclusion risks that aren’t solved just by saying “physical ID still exists” (Robles-Carrillo, 2024; Kudra et al., 2025; Naghmouchi et al., 2025).
Data Warehousing and Cross-Agency Integration
In New Zealand, the closest thing to a practical “data warehouse” for cross-agency integration has tended to show up through the Integrated Data Infrastructure (IDI) model: whole-of-population administrative datasets linked for research and policy use, with obvious analytical upside and equally obvious governance exposure. Greaves and colleagues lay out why the exposure lands unevenly for Māori: linkage magnifies the consequences of weak ethnic identifiers, deficit-framed research norms, thin community involvement, and shaky social license, and it also raises higher-stakes questions about consent, further linkage, offshore access, and whether Māori organizations face structural barriers to using the same system that produces narratives about them (Greaves et al., 2024).
That’s where “data warehousing” stops sounding technical and starts sounding like power. Te Kāhui Raraunga’s Māori Data Governance Model argues that existing government data practices often fail to meet Māori informational needs, It then pushes for governance settings that rebalance authority, build accountabilities, reduce data harm, and create meaningful benefit pathways. This includes investment in Māori data capacity and the option space for mana motuhake data infrastructure outside the public sector (Kukutai et al., 2023).
Read together, the message for any cross-agency integration program stays blunt: integration can scale insight, but it also scales harm unless Māori governance principles shape the rules, access conditions, and benefit design, and unless capacity gets funded as core infrastructure rather than treated like community “participation.”
Where Harm Surfaces
When people talk about harm the social defenses inevitably go up. Those in favor posture as if it's not a big deal, and paint those opposed as being irresponsible or lazy. Those opposed point towards systems in affected areas that are already dysfunctioning, as evidence that systemic reforms should be approached with caution. The discussion is loaded by nature. But that doesn't mean a discussion on harm should not be had. So let's look into the potential harms objectively.
Digital ID Standards Undermine Traditional Systems
Digital identity frameworks often start opt-in. The risk tends to appear later, when private vendors treat the fastest verification path as the default, then quietly penalize anything slower. That’s not a claim about NZ vendors already doing it. It’s a predictable pattern in digitized service environments: “choice” gets hollowed out when staff training, queue KPIs, fraud tooling, and customer impatience all reward the fastest channel.
NZ’s own digital exclusion evidence already shows why “channel choice” matters. CAB’s analysis of thousands of client enquiries frames digital exclusion as barriers created when services move online, and it explicitly calls out the importance of keeping other channels open so people can choose how they interact (CAB, 2020).
New Zealand coverage around the govt.nz app and planned “wallet” framing already signals a convenience-first direction, including use cases like showing a digital driver license to a bouncer, while still stating participation stays optional and physical ID remains available (1News, 2025; Mathias, 2025b; Radio New Zealand, 2025). That “optional but effectively unavoidable” drift shows up clearly in overseas mainstream reporting on digital-wallet identity rollouts, where privacy and rights groups warn voluntary schemes can become de facto mandatory through employer, vendor, and service design pressures, with the burden landing hardest on people dealing with digital poverty or lacking suitable devices (Booth, 2025; Rankin, 2025).
The same pattern also shows up in reporting that highlights practical barriers tied to device suitability and churn, including phones failing security requirements for new apps and large numbers of devices becoming unusable through network transitions, which turns “use the app” into a recurring cost and access problem rather than a neutral convenience feature (Mathias, 2025a; Mathias, 2025b).
The Digital Wallet Shifts the Cost Base
By shifting the cost base, a digital wallet model doesn’t eliminate identity overhead. It reallocates it. First, it pushes recurring operating costs onto individuals through device purchase and replacement, mobile plans, and the time cost of maintaining access. Then it pushes remediation and support costs onto the social layer, because when people can’t keep up with device churn, security requirements, or credential recovery, the work lands on whānau, caregivers, community providers, and often Māori institutions acting as the practical “last mile” interface.
- Individuals bear device cost, replacement cost, subscription cost, and the “always-on” expectation.
- When individuals can’t meet those requirements, community institutions absorb support load (help desks, identity recovery, advocacy, exception handling, training).
NZ research supports both layers.
- CAB identifies financial barriers, lack of device access, and affordability of connectivity as recurring blockers, plus literacy and disability barriers that don’t disappear just because a service has an app (CAB, 2020).
- InternetNZ’s “Out of the Maze” work, based on lived experience, describes digital exclusion as an interacting system of social and economic barriers, not a simple “teach them to click” problem. (InternetNZ, 2018),
- Work on older adults and smartphone training in NZ exists because the baseline problem persists. A course can improve competence, but the need for structured intervention tells you the market design isn’t self-correcting (Jaye et al., 2024).
In New Zealand, scholarship has described digital divides as multi-layered and materially real, with gaps tied to income, geography, age, and ethnicity, and with policy frequently under-integrating ICT needs into social safety design (Cotter, 2018). In aged residential care settings, research has found that facilities often publicize internet availability yet rarely provide devices, which leaves older adults vulnerable to exclusion from digital participation even when “online options” exist (Wrapson & Gasteiger, 2024). Work focused on Māori kaumātua during compounding crises has also surfaced barriers to telecommunications and digital technology, framing digital disparities as a live constraint on access and connectedness, not an abstract adoption lag (Wepa et al., 2025)
Now connect this to data sovereignty. If the state or major institutions push “iwi-controlled identity and data pathways” without resourcing, iwi and marae can end up paying twice:
- First as community support for excluded whānau dealing with digital systems.
- Then as governance actors expected to stand up policy, compliance, cybersecurity, vendor review, and audit capacity.
International research on digital identity wallets has started confronting the gap between security, usability, and discrimination risk, including how “secure-by-design” can still produce exclusion in practice if it doesn’t match real social conditions (Kudra et al., 2024; Kjørven, Gjøsteen, & Wærstad, 2025). Research on national digital identity systems also emphasizes that legal frameworks and data protection controls don’t automatically settle the core design challenge: aligning identity infrastructure with human realities and societal risk (Naghmouchi et al., 2025).
The real risk here is when frontline vendors prefer app-based verification because it’s faster and reduces staff judgment calls, then analog pathways can become nominal, in spite of recognized gaps. Formal policy can say “paper remains accepted,” while market behavior quietly shifts toward “app or delayed service,” and disadvantaged users pay the time, hassle, and refusal penalties.
That looks like empowerment on paper, but it operates like an unfunded mandate.
Identity Systems Defer Responsibility to Individuals
Digital identity and wallet systems often get sold as fraud-reducing infrastructure, but they also create new failure modes that don’t look like classic “forgery.” Practical control can break down under coercion, social engineering, low digital capability, disability, and day-to-day reliance on third-party assistance, and “sole control” frameworks can turn that messy reality into a legal and social expectation that the individual should have prevented the harm (Kjørven, Gjøsteen, & Wærstad, 2025).
That shift matters because it changes the story after an incident: instead of treating misuse as a predictable ecosystem risk, the burden slides toward “why didn’t you manage it properly,” which can translate into exclusion and reputational damage for groups already dealing with unequal digital conditions (Kjørven, Gjøsteen, & Wærstad, 2025). Usable-security research on wallet prototypes reinforces the same friction from a different angle: users can misunderstand wallet behaviors and disclosures, and UX and security can undermine each other, which increases the chance that “secure-by-design” still fails in practice for normal people under normal pressure (Sauer et al., 2025).
Revocation then becomes a real-world stress point, because wallets don’t just need strong issuance and presentation. They need reliable ways to prove a credential is still valid or has been suspended or revoked, without turning routine checks into privacy leaks or operational chaos (Germenia et al., 2025). The technical literature on wallet ecosystems treats revocation-status checking as a core design problem with trade-offs around privacy, scalability, and interoperability, which lines up with the lived reality that loss of control isn’t rare, and recovery needs to be assumed rather than treated as edge-case user error (Bureacă et al., 2025; Germenia et al., 2025).
By deferring responsibility of credential validity onto individuals the government is essentially washing their hands of meaningful involvement as a neutral third party. When it comes to identity, acting as an independently recognized, valid third party is the function of government. If the government is not ensuring the wellbeing of its people at a basic level of identity, what exactly is it doing? Other than collecting taxes of people it disavows any functional knowledge of.
Data integration Increases Surveillance Optics
Large-scale administrative data integration tends to make populations more “legible,” meaning easier to classify, compare, and act on from a distance, and that legibility can expand state and institutional capacity even when the public pitch is service access and inclusion (Scott, 1998). Digital ID systems sit naturally inside that logic because they standardize identity attributes and linkages, producing “machine-readable” people whose complexity gets compressed into institutional categories, and that compression has a track record of reproducing structural inequalities while still being framed as modernization (Yahaya & Nyamwire, 2024). Empirically, digital ID expansion can even attract broad support among historically marginalized groups, which is exactly why “inclusion branding” doesn’t settle the governance risk, since the downstream consequences of legibility still distribute unevenly (Garbe et al., 2024).
In Aotearoa, Māori-focused scholarship on the IDI argues that population-scale linkage raises Māori-specific governance issues around deficit framing, access, control, and benefit, and those tensions don’t disappear just because the system is de-identified and research-oriented (Greaves et al., 2024). Indigenous data governance work on linkage makes the underlying point explicit: administrative data has historically been collected to serve government agendas and can default to deficit-focused interpretations unless Indigenous governance shapes the rules, access pathways, and interpretation layer (Reeve et al., 2024).
You don’t need to assume malicious intent. You just track incentives: fraud reduction, cost reduction, automation, and “digital first” convenience can dominate, and the communities with the least capacity get hit hardest by brittle edge cases (Kukutai, 2024).
“Māori Governance Involvement” Becomes Consultation Theater
Consultation theater shows up when Māori participation gets structured as advice, cultural input, or “engagement,” while the core levers stay elsewhere: rule-setting authority, veto or pause rights, budget control, compliance enforcement, and liability allocation.
Participation scholarship has treated this pattern as a predictable failure mode for decades, because voice without delegated authority tends to legitimize decisions that were always going to be made, then uses the presence of consultation as proof of fairness after the fact (Arnstein, 1969). In digital identity settings, advisory structures can still improve cultural alignment and reduce unforced errors, but the governance risk persists when advice can be accepted, narrowed, deferred, or ignored without consequence, especially under delivery incentives like speed, fraud reduction, and “digital-first” convenience.
The next step in the failure chain comes from where operational burden lands. “Digital identity” and “wallet” programs generate a constant tail of exceptions: lost devices, caregiver control, coercion dynamics, low digital capability, supervised-care realities, credential recovery, and frontline vendor refusal or inconsistency. If Māori institutions are treated as the practical last-mile support layer, they end up carrying the social fallout and training load, even when they don’t control standards, accreditation rules, or enforcement. Māori Data Sovereignty principles explicitly treat governance as requiring capability and workforce development, because control without resources stays symbolic and fragile (University of Otago, 2018).
Māori governance models also emphasize that data harms and benefits distribute through institutional design, not just through stated intent, so “partnership” that doesn’t fund capability can recreate the same asymmetry it claims to address (Kukutai et al., 2023).
The risk intensifies once identity infrastructure sits inside linked administrative data and automated decision systems, because custody and consent don’t capture where many harms actually occur. Population-scale linkage systems can amplify deficit framing and power imbalance unless Māori governance shapes access rules, purpose boundaries, interpretation norms, and benefit pathways, and unless Māori organizations can participate as genuine system actors rather than external stakeholders (Greaves et al., 2024; Theodore et al., 2023). Algorithmic sovereignty work pushes the same point in more direct operational terms: the governance problem moves downstream into decision logic, proxies, triage rules, and automated classifications that can harden inequities while still appearing administratively “neutral” (Brown et al., 2024).
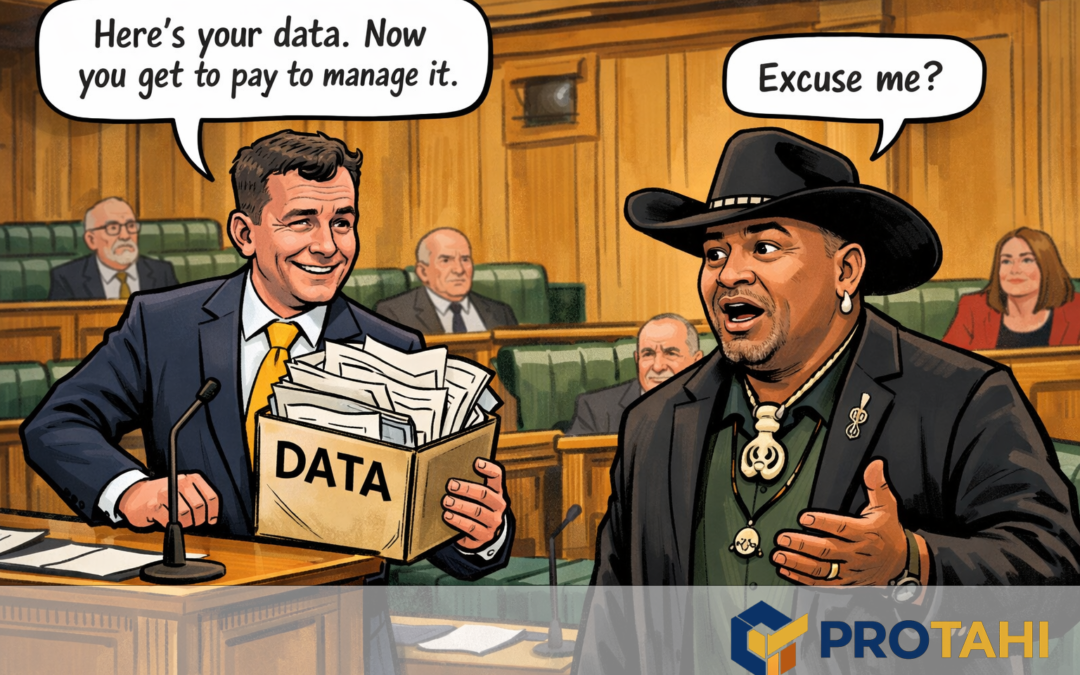
Data Sovereignty then become a rhetorical shield. The device is simply "You asked for sovereignty. So here's your data. Go be sovereign with it." The language signals compliance, while the actual system continues to centralize authority and outsource friction through failure to meaningfully support outcomes.
Stopping this from Becoming Another Failure Narrative
In evaluating techology policy or a rollout, these are the non-negotiables that block cost-shift and exclusion dynamics:
- Hard offline equivalence
Not “we still accept physical ID.” Instead: vendors and agencies must support offline pathways with equal legal validity, predictable turnaround, and anti-discrimination enforcement. CAB’s emphasis on real channel choice supports this. - Device and connectivity burden gets treated as a policy cost, not a personal lifestyle choice
If a credential system assumes smartphones, then subsidy and replacement pathways need to exist for low-income users, elders, and people in supervised care, or the system quietly becomes a regressive tax. - Identity recovery and exception handling must be funded as core infrastructure
Recovery becomes the hidden tax. Someone pays. If the state doesn’t, iwi and community organizations will, through time, staffing, and stress load. - Governance power needs enforceable levers, not just advisory presence
Advisory groups help with legitimacy, but harm prevention needs veto points, rule-setting authority, auditing access, and the ability to pause deployments that fail equity tests. - Data sovereignty commitments must come with sufficient capability investment and a clean transfer path
Te Mana Raraunga’s principles set a high bar for control across the whole lifecycle of Māori data. That bar implies resourcing. Without it, the state effectively hands Māori institutions a responsibility they can’t realistically carry.